Last updated at Thu, 21 Jan 2021 15:49:12 GMT
It goes without saying that the 117th US Congress has a lot to get done and many legitimate priorities are competing for finite legislative attention. Cybersecurity will be in this mix. In the wake of the SolarWinds attack, President-elect Biden issued a statement emphasizing that his Administration will make cybersecurity “a top priority at every level of government.” Vice President-elect Harris was a leader on consumer privacy protection during her time as California’s Attorney General. Given the Democrat-controlled Congress, the multiple privacy/security bills filed in many past legislative sessions, and continued action by states such as California and Washington, businesses should anticipate another push for federal private sector privacy and security legislation in the upcoming Congress. (Whether such legislation actually passes, given the mix of other priorities, is another matter!)
[Check out our past blog post on updating state data security laws.]
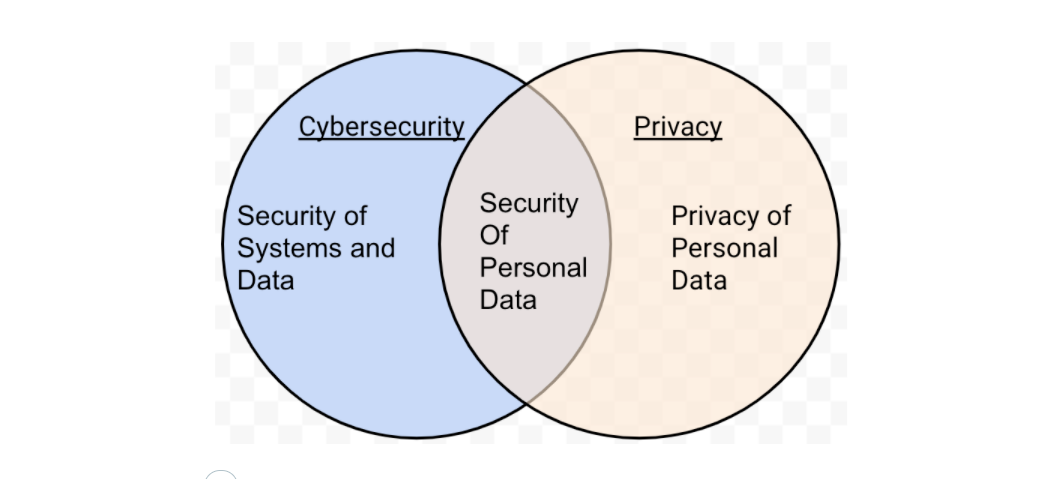
Rapid7 welcomes this effort. Congress should pass legislation requiring security of personal information nationwide, independent of breach notification, either as a standalone or as part of comprehensive privacy legislation. We believe consumers and businesses will benefit from uniform rules on data protection, rather than the growing patchwork of state and international privacy regulations. Although security of personal information is only one slice of the broader issue of cybersecurity, it is one that directly affects many individuals, and the ripple effect of requirements to secure personal information will help raise the overall bar on the security of other systems and entities.
While any federal privacy and security legislation must accommodate a broad diversity of organizations, it must also be effective and not take a significant step back from protections consumers have today. To that end, as we aim to strike that balance, we suggest the below high level principles on personal information security legislation.
What we look for in personal information security legislation
1. Effective security requirements.
Require private sector entities to implement reasonable security processes for personal information they collect, store, maintain, or transmit (AKA “personal information security”) to protect the security of personal information against unauthorized acquisition and access. The requirements should be:
-
Flexible. To avoid a disproportionate burden, the security program should be flexible to accommodate a diverse range of organizations. These considerations can include the size and complexity of the covered entity, the sensitivity of the personal information, the state of the art in security protection, and material cybersecurity risks and threats.
-
Built around key security program elements. To keep pace with evolving threats for a diversity of organizations, required security elements should be risk-based. However, legislation should specify that the security program must include high level elements based on standards, best practices, and existing regulations such as GLBA and HIPAA. We believe those elements should include:
- Designate staff. Designate employees to coordinate the security program, ensure they have adequate resources and training.
- Risk assessment. Assess material internal and external risks, threats, and vulnerabilities to security of personal information. Periodically reassess.
- Security controls. Implement physical, technical, and administrative safeguards reasonably designed to control risks identified through the risk assessment. Inclusion of “reasonably” is helpful to ensure the controls are objectively commensurate with the risks.
- Monitoring and testing. Regularly test and monitor the effectiveness of safeguards.
- Service providers. Oversee service providers’ implementation of security safeguards.
- Incident detection and response. Develop and implement written plans to detect, respond to, and recover from cybersecurity intrusions, events, and incidents.
-
Not limited to financial harm. Security requirements should not be limited to protecting against financial, physical, or “substantial” harm. This common loophole would be severely limiting and out of step with user expectations, the wide array of threats organizations face, and many state laws (see, e.g., CA, FL, NY, TX).
2. Security exemption from privacy restrictions.
Privacy law and legislation tend to include a series of exemptions for publicly beneficial purposes, such as public safety (see, e.g., GDPR) If security is folded into privacy legislation, it is important to avoid impeding cybersecurity by exempting activities necessary for security from privacy restrictions. For example, a privacy requirement to obtain consent to share personal information should not apply in a situation where a covered entity detects a phishing attempt and shares the phishing email with other companies or an ISAC to help prevent successful phishing.
- Scope. The security exemption should cover activities for prevention, detection, and response of cybersecurity incidents and threats. Security should be exempt from a broad range of privacy requirements, rather than just a limited subset, to be most effective.
3. Preemption without undermining cybersecurity.
The issue of whether federal rules should preempt state laws is hotly contested, and a major challenge to the progress of past privacy and security legislation. (Rapid7 supports preemption of state security laws with a strong national standard to provide consistent protections to consumers and because complexity hinders compliance.) For purposes of these principles, we are focusing here only on ensuring that any federal preemption avoids undermining other cybersecurity laws, rules, and standards that are not directly related to personal information security. Examples of state rules that should not be preempted by a federal personal information security law include system security requirements, IoT and critical infrastructure security standards, government procurement requirements, computer crime and wiretapping laws, etc.
- Scope. Rapid7’s recommendation is to preempt state laws, regulations, and rules having the force of law (not standards without the force of law) that require covered entities (as defined in the legislation) to secure personal information (as defined in the legislation). An example of legislation with an overly broad preemption provision that does not meet this framework, and may undermine cybersecurity, is the SAFE DATA Act of 2020 (S.4626, Sec. 405).
In an effort to be relatively brief, we won’t attempt to cover all the nuance and context for information security legislation (like the much-contested definition of “personal information”). Instead, the above focuses on a few security-specific sticking points that we believe are worth emphasizing based on our experience in working on past legislative efforts.
Worth consistent protections
Federal personal information security legislation is past due, as every year of delay tends to see uncoordinated growth in state and international privacy and data security regulations. Nonetheless, we should temper our expectations about the chances of federal privacy or security legislation crossing the Congressional finish line in the next two years amid competing priorities. Still, we are confident personal information security requirements will be revisited and worked on again during the 117th Congress, and the above principles will help guide Rapid7’s response.
