Last updated at Wed, 17 Jan 2024 01:02:01 GMT
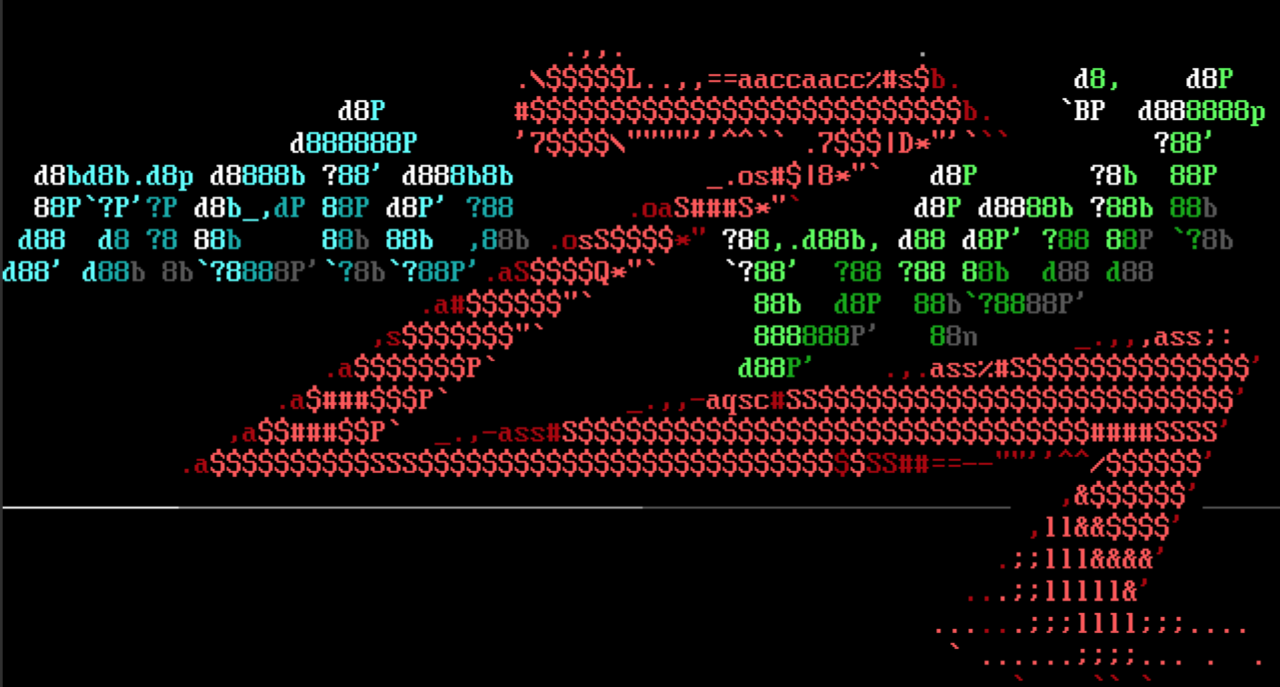
elFinder remote command injection
elFinder is a client-side open-source file manager tool written for web applications. In a browser it has the look and feel of a native file manager application. It ships with a PHP connector, which integrates the client side with the back end server. The connector provides the ability for unauthenticated users to upload an image and resize it. It does so by shelling out to the exiftran command line utility. Filenames, however, are not sanitized for shell metacharacters, which can be used for remote command injection. bcoles added a Metasploit module to exploit this vulnerability (CVE-2019-9194). elFinder versions 2.1.47, 2.1.20 and 2.1.16 have been tested on an Ubuntu system.
Fortinet SSL login scanner
A recent analysis of HTTPS endpoints discovered by Project Sonar showed over 120k IPv4 endpoints that are likely Fortinet FortiGate devices where the SSL VPN is known to be in use. mcmichels added a scanner module that tests credentials on FortiGate servers through web login portals. It checks to see if the portal is backed by a FortiGate server before it performs a brute force login attempt. The module supports multiple host scanning, IPv6, and realm/domain specification.
Total traversal
fabiocogno contributed an auxillary scanner module that checks and exploits a directory traversal vulnerability (CVE-2019-8903) in Total.js, a Node.js framework for building web applications. This Metasploit module can read and download files from a vulnerable web server. It provides the ability to set the traversal depth and supports over 40 different file extensions such as .jpg, .xls, and .mp4. Total.js versions prior to 3.2.4 are affected.
Overheard in the Metasploit office this week
Haven't we all had a run in with the demo gods?
"Funny thing happened on the way to the demo meeting. I had rebooted my test machine, possibly because of a syrup / french toast incident at breakfast this morning. Subsequently, Ruby started segfaulting in my environment in the postgresql gem."
I hear this as a hacker haiku.
"It really is an elegant and disastrous replace-the-shell-command-with-something-more-evil example of aggressive compiler optimizations against undefined behavior."
In response to a puzzling matter...
"I don't really, either. Maybe something about tedious work with tools that seem needlessly Byzantine?"
New modules (3)
- elFinder PHP Connector exiftran Command Injection by Thomas Chauchefoin, bcoles, and q3rv0, which exploits CVE-2019-9194
- Fortinet SSL VPN Bruteforce Login Utility by Max Michels
- Total.js prior to 3.2.4 Directory Traversal by Fabio Cogno and Riccardo Krauter, which exploits CVE-2019-8903
Improvements
- PR 11559 by jrobles-r7 fixes the
checkcommand to use the value ofRHOSTSwhen none are directly passed to the command. - PR 11558 by h00die adds Ubiquiti UniFi platform detection to the SSH LoginScanner.
- PR 11557 by h00die adds the Ubiquiti default credentials to the router credentials wordlist.
- PR 11551 by busterb fixes a regression in which auxiliary modules could no longer run as a background job.
- PR 11544 by busterb adds the ability to easily disable the standard datastore options when including TCP and UDP mixins.
- PR 11061 by asoto-r7 adds the possibility for string values in module options to be the empty string.
Get it
As always, you can update to the latest Metasploit Framework with msfupdate and you can get more details on the changes since the last blog post from GitHub:
We recently-announced the release of Metasploit 5. You can get it by cloning the Metasploit Framework repo (master branch). To install fresh without using git, you can use the open-source-only Nightly Installers or the binary installers (which also include the commercial editions).