Last updated at Mon, 08 Oct 2018 13:02:01 GMT
A day in the life of an application security professional is no walk in the park. Scans, more scans, vulnerabilities, and software development teams are running at a breakneck pace, making deployments a daily exercise. Complex web application security testing programs must cater to this rapid pace of change by utilizing flexible tools that can integrate seamlessly into multiple environments.
To help with this challenge, we are pleased to announce the newest addition to your application security toolkit on the Rapid7 Insight platform: the public API in our DAST solution, InsightAppSec.
Uncover security vulnerabilities in your web apps today! Sign up for a free InsightAppSec trial.
Get StartedAPI == Game Changer
We’ve all been there. You find an application that fits into your workstream and gets the job done for a specific use case. There are a few limitations you can work around, but sooner or later, you find something you just can’t do. Missing features may be technically achievable, but some things just aren’t possible as a logged-in user navigating the onscreen controls. To attempt to automate an operation using some type of conditional logic would basically need some form of magic to make it a reality.
That magic is an application programming interface (API), which allows a user, script, or another toolset to interact directly with an operation within an application. Though API formats have changed dramatically over the years as standards and supporting toolsets have been introduced, their use case—interacting with a software application without interacting with a UI—remains fundamentally the same.
For InsightAppSec, this means you can build new apps, run scans with configurations built on the fly (e.g., using dynamically generated credentials), check the status of a scan in progress, and cancel a scan based on some external check.
Let’s look at a few examples:
Updating vulnerabilities
Let’s face it, web application security scans can return a bunch of information, and being able to distill this down into an actionable plan is the cornerstone of any security program. With the InsightAppSec public API, you can retrieve information on vulnerabilities and start pushing changes programmatically. Using your favorite API development environment, such as Postman, it’s easy to update the severity and status of a vulnerability you’re interested in.
Pulling a list of all vulnerabilities is as simple as entering the following:
GET /ias/v1/vulnerabilities
This will show you a response similar to the following:
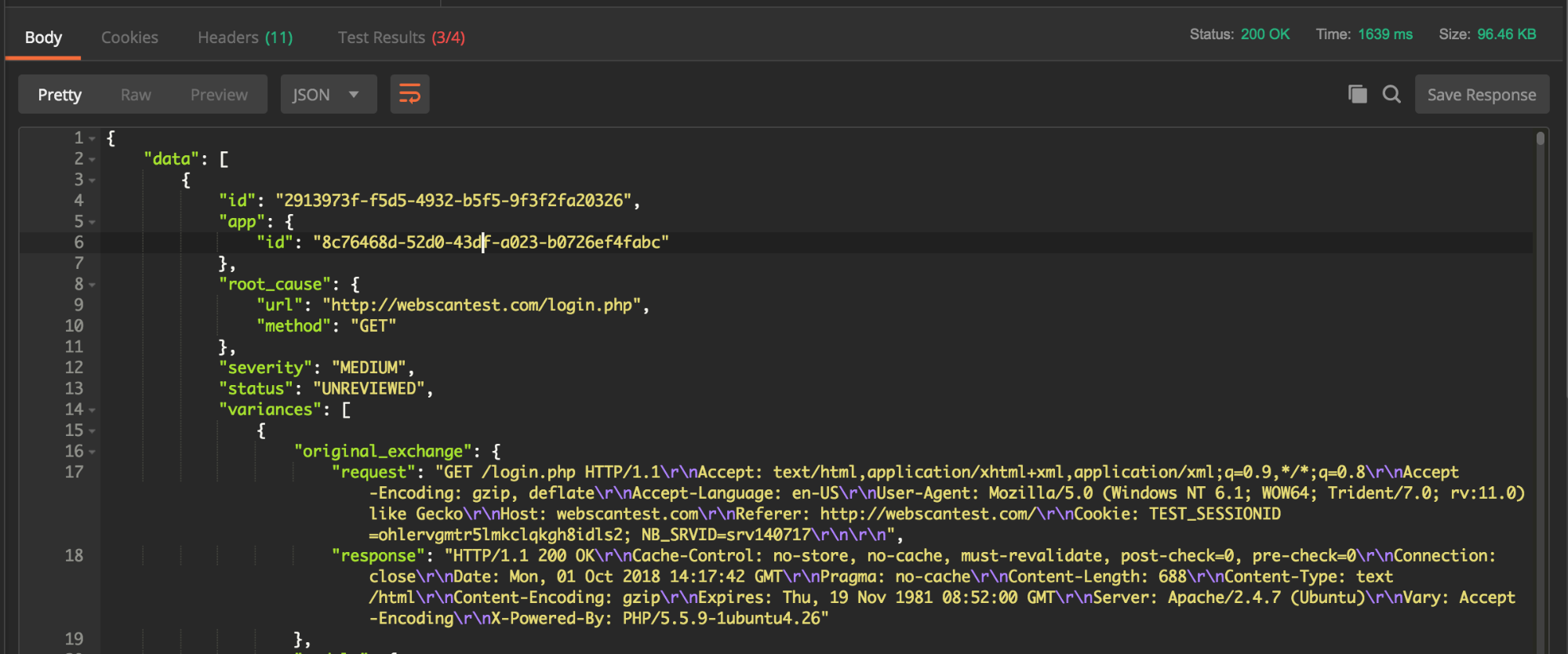
From here, if you grab an individual vulnerability ID, you can easily push changes to that vulnerability to update its severity and status:
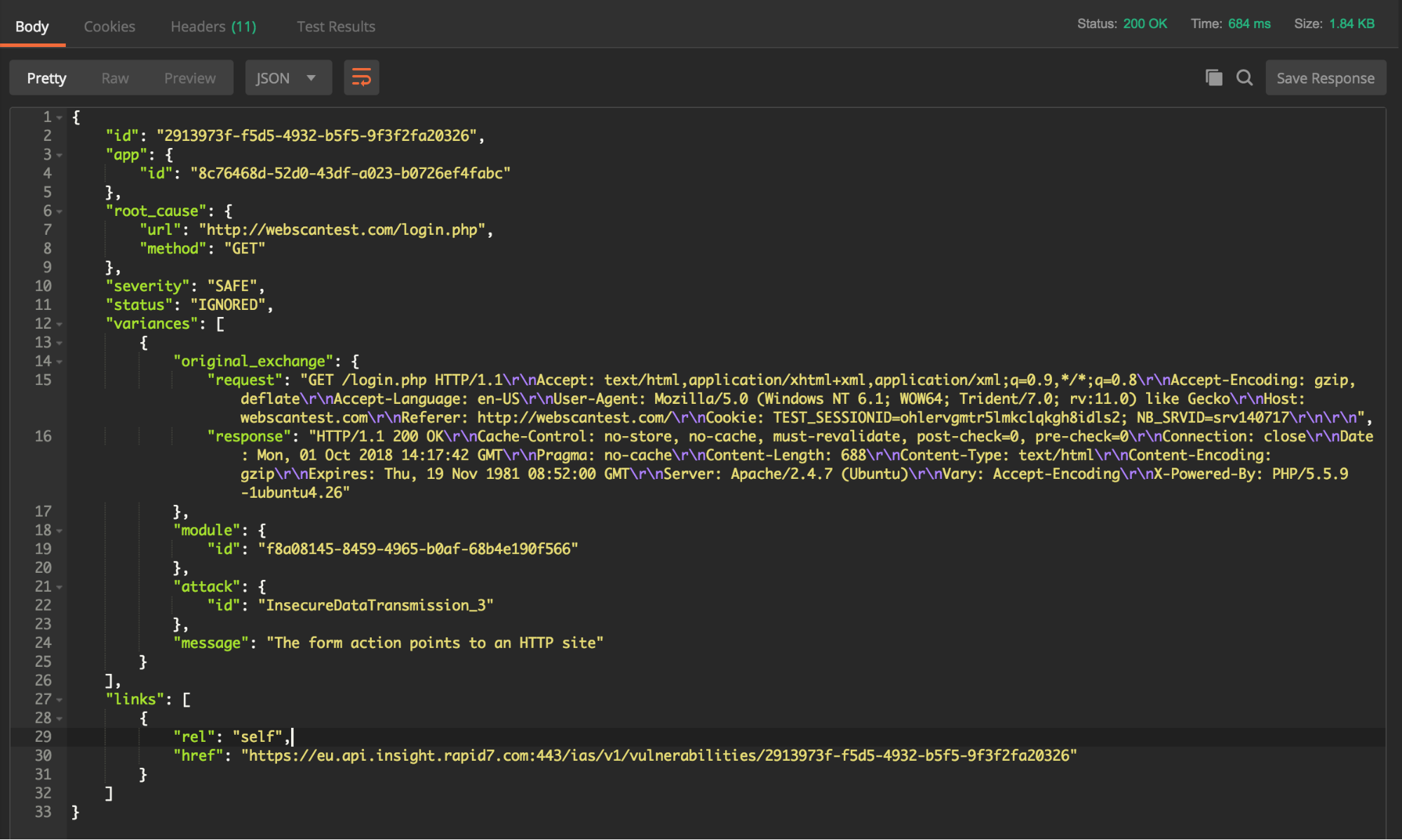
PUT /ias/v1/vulnerabilities/2913973f-f5d5-4932-b5f5-9f3f2fa20326
Host: eu.api.insight.rapid7.com
X-Api-Key: {{X-Api-Key}}
Content-Type: application/json
Cache-Control: no-cache
{
“severity”: “SAFE“,
“status”: “IGNORED”
}
A quick follow-up check will show the change was successful, with a 200-response code:
GET /ias/v1/vulnerabilities/2913973f-f5d5-4932-b5f5-9f3f2fa20326
Updating authentication settings
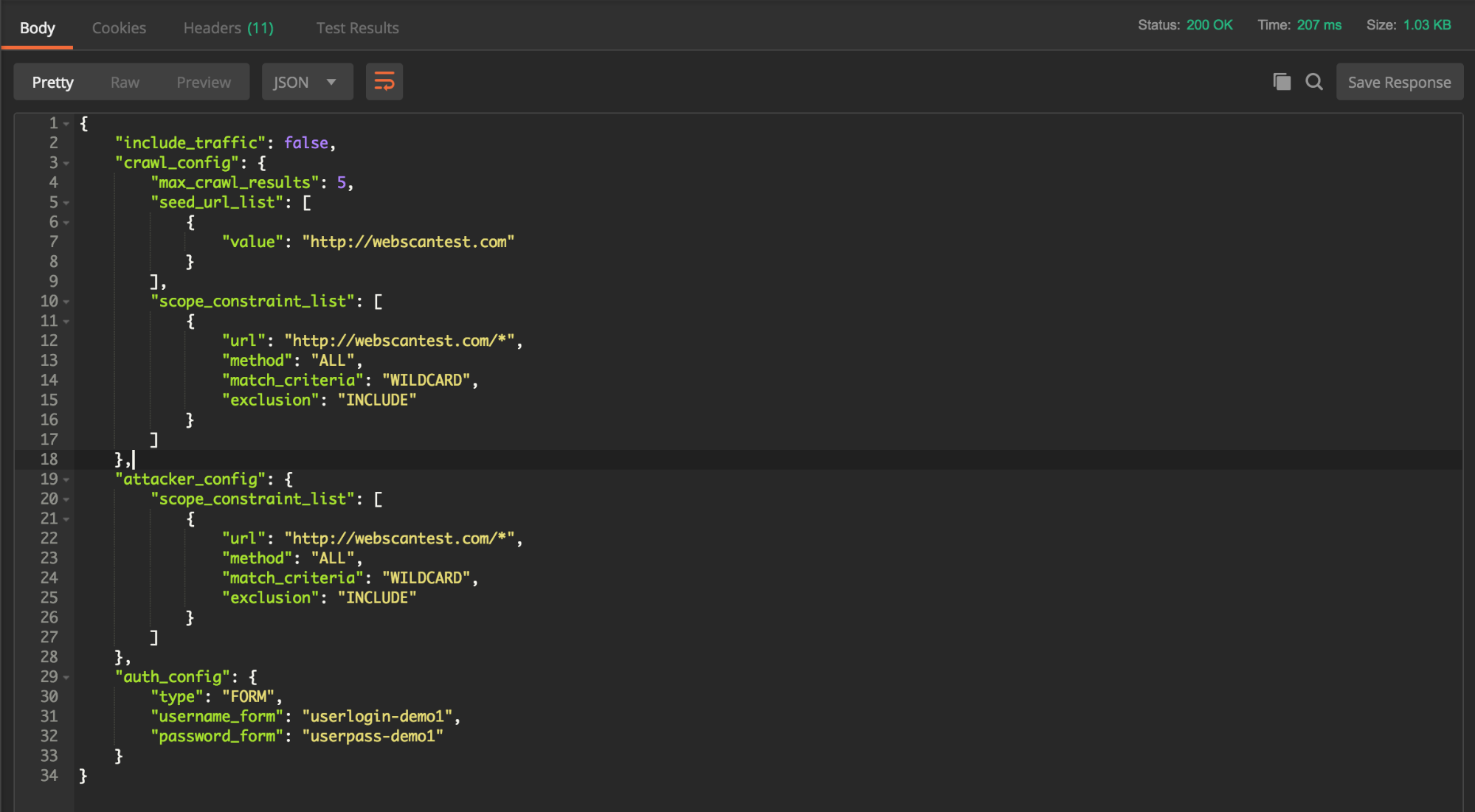
Likewise, if you find yourself using rolling credentials for your authenticated scans, you can easily use the API to update those settings everywhere they are used. With the ID of the scan config, you can easily push changes as follows:
PUT /ias/v1/scan-configs/1c121e12-1c10-41a4-9739-9592611a20b3/options
Host: eu.api.insight.rapid7.com
X-Api-Key: {{X-Api-Key}}
Content-Type: application/json
Cache-Control: no-cache
{
"include_traffic": false,
"crawl_config": {
"max_crawl_results": 5,
"seed_url_list": [
{
"value": "http://webscantest.com"
}
],
"scope_constraint_list": [
{
"url": "http://webscantest.com/*",
"method": "ALL",
"match_criteria": "WILDCARD",
"exclusion": "INCLUDE"
}
]
},
"attacker_config": {
"scope_constraint_list": [
{
"url": "http://webscantest.com/*",
"method": "ALL",
"match_criteria": "WILDCARD",
"exclusion": "INCLUDE"
}
]
},
"auth_config": {
"type": "FORM",
"username_form": "userlogin-demo1",
"password_form": "userpass-demo1"
}
}
After you push, the new credentials will be saved and utilized the next time you kick off a scan on your app. Need more than one scan config using the same credentials across a bunch of apps? No problem! Just grab the scan config ID for each one and push the same change. This could also be automated with an appropriate integration into your credential security management systems.
To verify the change and see that your new settings have been applied successfully, follow this up with a GET on the just-updated scan config:
GET /ias/v1/scan-configs/1c121e12-1c10-41a4-9739-9592611a20b3/options
Documentation
API documentation is essential to understanding the capabilities supported and the information that needs to be sent with requests in order to ensure success. Not only did we upload this as an interactive help doc, but we also baked it right into the product. Within InsightAppSec, the menu at the top of the page includes a link to the API documentation right alongside the “Help” option.
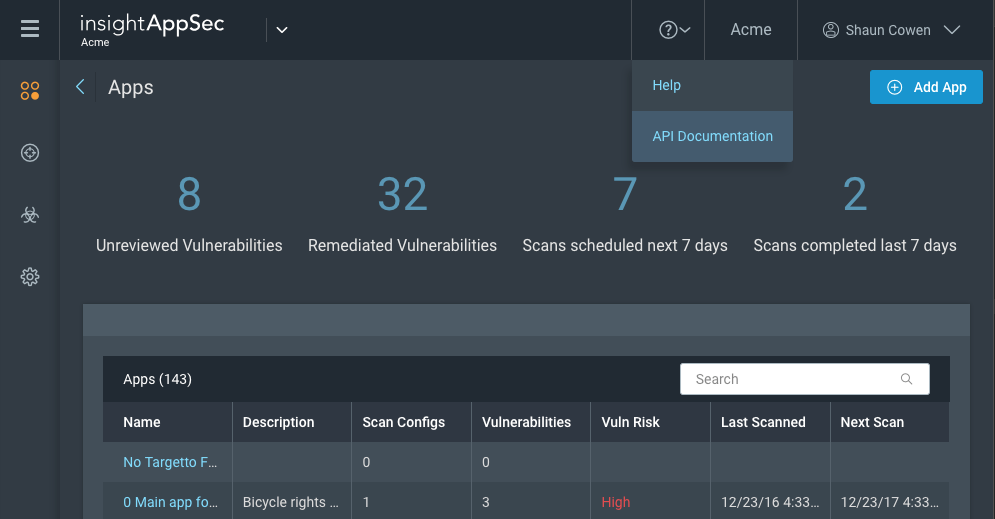
That link will take you to our InsightAppSec API documentation page, which offers helpful guides and examples to get you up and running with the public API.
These guides are broken out into functional sections and will be updated automatically as we roll new features into the API.
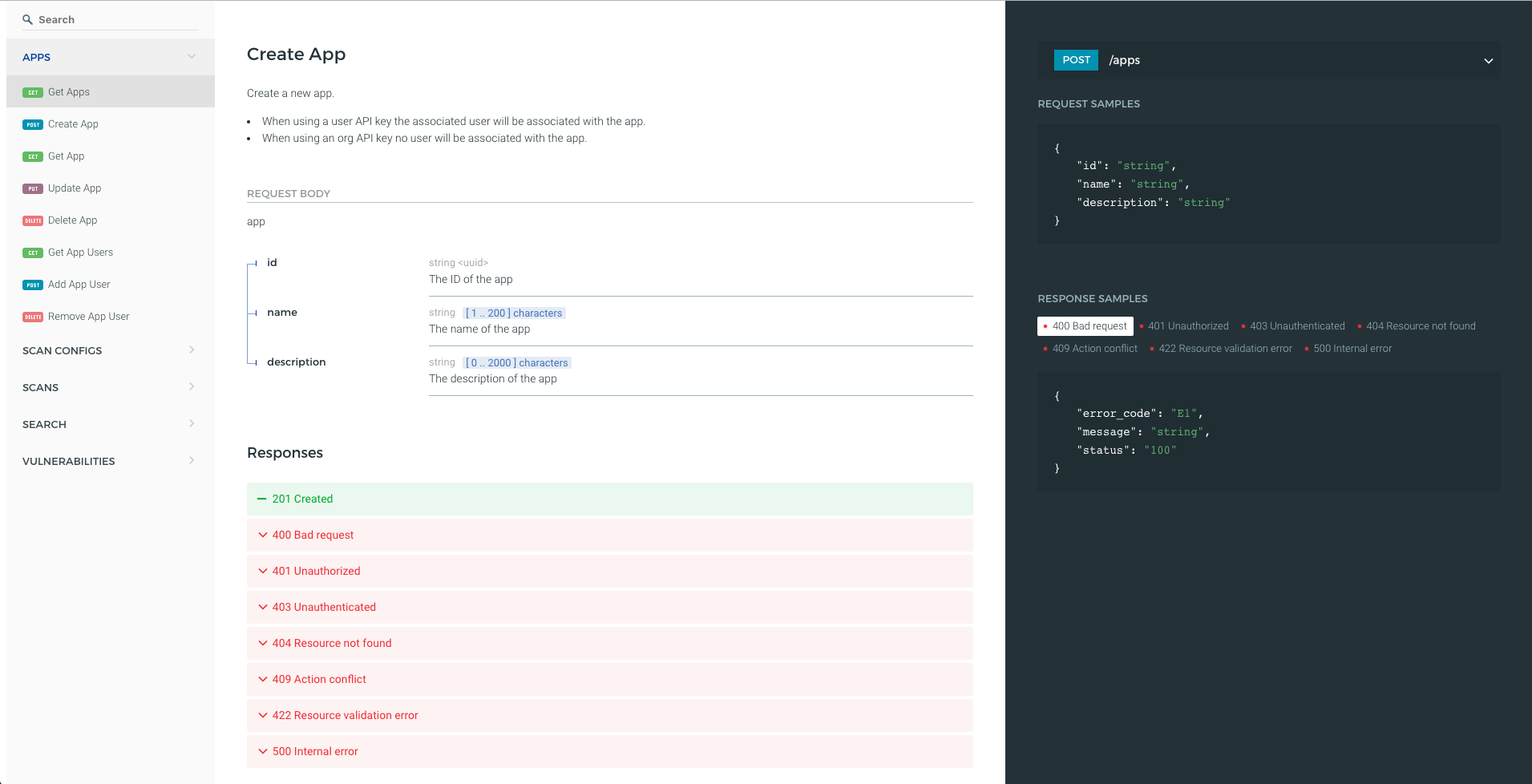
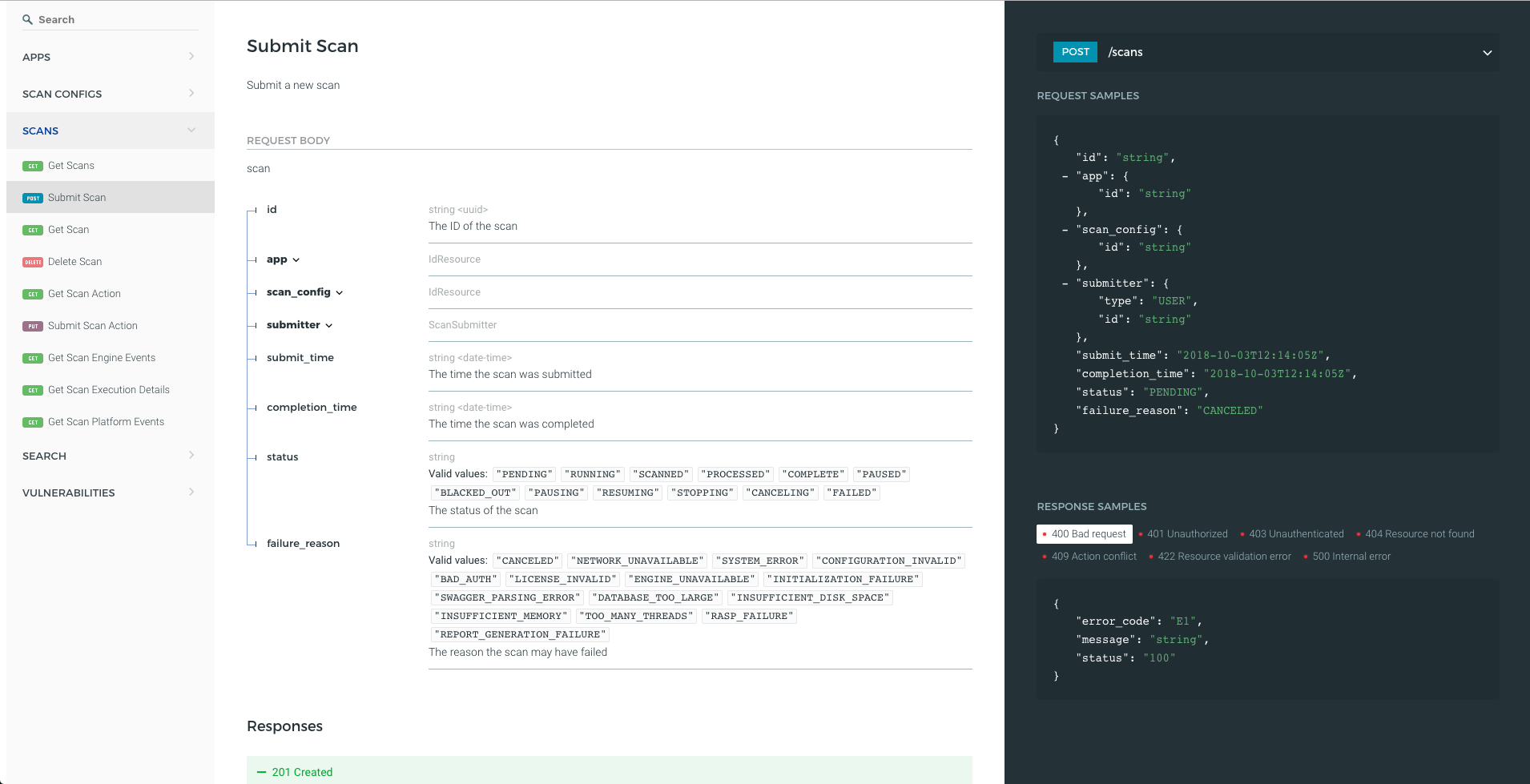
Let’s look at some examples of what you need to create your first app and start your first scan:
Still have questions? Get in touch today and see what Rapid7 can do for your application security program!
More on InsightAppSec
InsightAppSec brings Rapid7’s proven Dynamic Application Security Testing (DAST) technology to the Insight platform, combining powerful application crawling and attack capabilities, flexibility in scan scope and scheduling, and accuracy in results with a modern UI, intuitive workflows, and sensible data organization. This enables you to identify cross-site scripting (XSS), SQL injections (SQLi), cross-site request forgery (CSRF), and other common web application vulnerabilities with ease. The best part? All of these capabilities are delivered via the cloud, so you are up and running in as few as five minutes to identify the critical security risks in your applications.
