Last updated at Wed, 07 Feb 2024 19:22:40 GMT
We’ve added a new option to the smb_lookupsid Metasploit module. You can now specify your starting RID.
Wait, What Does This Module Do Again?
As a penetration tester, one of the first things I try to do on an internal network is enumerate all of the domain users so that I can perform login attacks against them. It would be a noteworthy risk if we could do that anonymously, because that means that any malicious actor who can connect to an affected system can obtain a list of users without being authenticated. To check for anonymous user enumeration, I would start with something like the smb_enumusers and smb_enumusers_domain Metasploit modules, or rpcclient and enum4linux to check for null sessions.
If I don’t have any luck with null sessions, my next step would be anonymous SID-to-name translation with the smb_lookupsid module. I use this as a secondary option because it’s going to be slower than null sessions.
So what are SIDs and what are we doing with them? Users, computers, security groups, and other security principals on NT-based systems each have a unique Security Identifier (SID). If you rename a user account, such as your default Administrator, it still uses the same SID. The SID contains a Relative Identifier (RID) that is unique to each security principal within a given domain or local system. For example, the default Administrator account in a Windows domain or on a local workstation has a RID of 500. The smb_lookupsid module lets us ask target hosts to resolve a range of RIDs, starting with 500 and ending with our MaxRID option value, to their usernames.
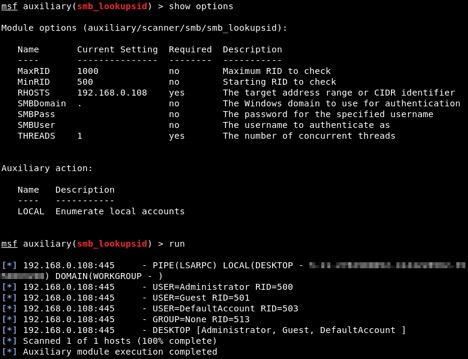
Here’s an example of using smb_lookupsid for local user enumeration against a test system, with the MaxRID option set to 1000:
From the perspective of a penetration tester, it’s ideal if we can do this anonymously. However, it can also be useful if we can get our hands on a set of credentials in another way, but still want to get a list of all domain users for login attacks. I might get one set of credentials from LLMNR poisoning and password cracking, or find some training account login credentials written on a whiteboard in a training room. I can now use the credentials I do have with the same tools I tried for null sessions, or with SID-to-name lookups.
When a Starting RID is Useful
When starting a test, we don’t know how many users there are in the domain. While we know that the RIDs for built-in accounts are going to start at 500, and RIDs for non-default objects are going to start at 1000, we don’t know where they are going to stop. A domain has a RID master, which allocates pools of 500 RIDs to each domain controller that will each request another block of RIDs when they begin to run low. RIDs numbers will often get up into the tens of thousands, usually with many small and large gaps in between them. Starting with Windows Server 2012, the maximum number of RIDs is a little less than 2.15 billion.
By default, smb_lookupsid has a MaxRID value of 4,000. Personally, I might start by setting that to anything from 20,000 to 50,000, depending on my own gut feeling about that network and various factors like how long the domain has been used, how big the organization is, and so on.
So I might start by trying to resolve RIDs 500 through 20,000. However, if I notice that there are still a lot of users coming back towards the end of that, I’ll want to go back and run from 20,000 to 50,000.
Previously, this would mean starting from 500 again. Now, with our MinRID option, I can pick up from where I left off and resolve 20,000 to 50,000 instead.
Demonstration
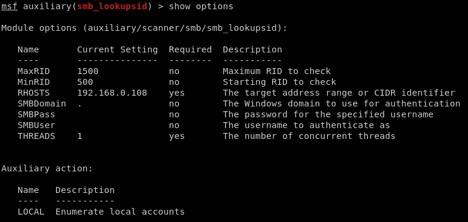
We’re going to do some anonymous user enumeration against a test system, for local user accounts. Since RIDs for non-default security principals start at 1,000, and we’re not expecting there to be hundreds or thousands of local users on a system, we’ll start with MaxRID set to 1500:
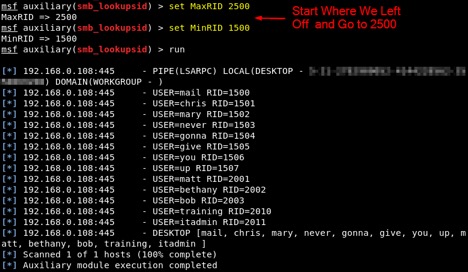
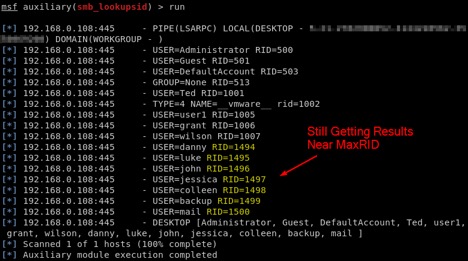
Looking at our results, that assumption about the MaxRID appears to be wrong. We’ve got several users coming back towards the end of our range:
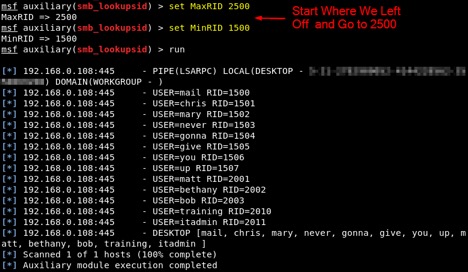
If we wanted go back and look for users through RID 2500, we used to have to set our new MaxRID and start from 500 all over again. Now, we can set MinRID to 1500 and pick up where we left off:
So there we have a little refresher on smb_lookupsid, and an example of how this new MinRID option can be used in a practical, real-life situation. Happy hacking!