Last updated at Fri, 29 Jun 2018 14:01:10 GMT
It was just a few months ago when we launched our beta program. And with beta users working within our security orchestration and automation platform, we built out new features, refined others, and overall fortified our solution.
We validated that security teams not only want to save time, increase productivity, and streamline operations, they also need a tool that would allow them to add automation to their security workflows as fast as possible, and without the need for code.
So, with much excitement, the Komand team is proud to announce our security orchestration and automation platform is launching out of beta for all to use!
The general availability of Komand means teams can now connect their security services, and automate their time-intensive processes faster than ever before.
And with the official closing of our seed round, we can continue to provide security teams with much needed relief from tedious, manual security tasks and processes.
Powerful Orchestration, Seamless Automation
We know firsthand how frustrating it can be to work with unintegrated systems and time-consuming, manual processes (e.g., incident response, threat intelligence, vulnerability assessments, and more).
We built Komand to help security teams connect their systems and automate tedious tasks. With the gains in productivity we enable, security professionals can use their expertise to respond to security events faster and with better accuracy. And without the need to code, resource-strapped teams can focus on the most strategic aspects of the security equation.
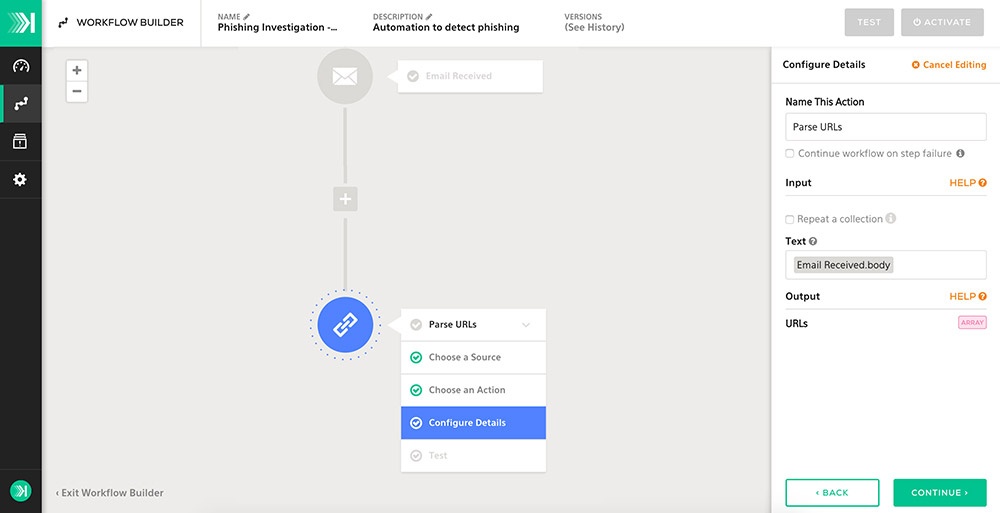
Komand acts as an orchestration layer to help companies gain more value from their current suite of security tools. Robust plugins allow teams to integrate tools with dynamic workflows that automate tedious tasks, while still employing human decision-making when necessary.
How do we do this? Using Komand, security teams benefit from:

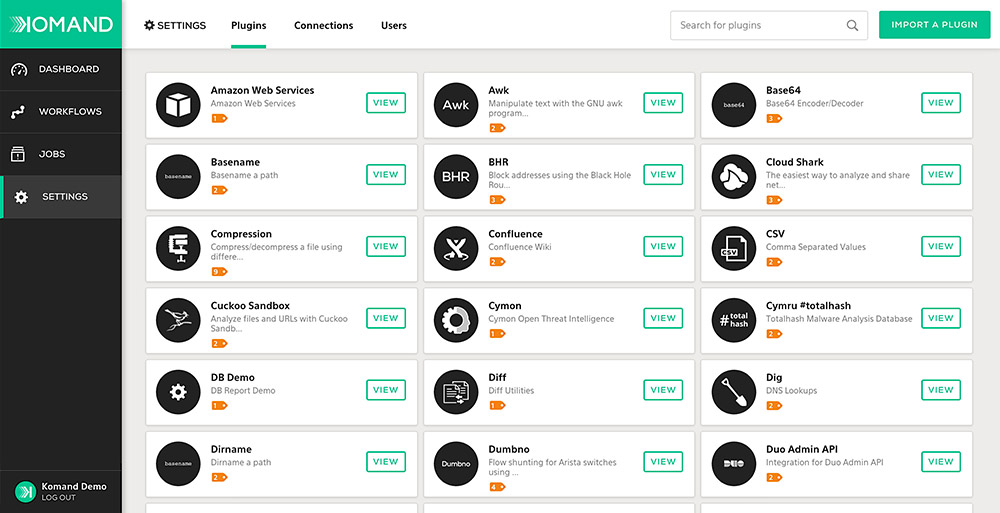
An Integrated and Extensible System
With our plugin library, you can connect all your existing tools. We also have a plugin SDK if you want to build your own. (Psst. As of this week, we support 90 plugins, with over 180+ actions.)

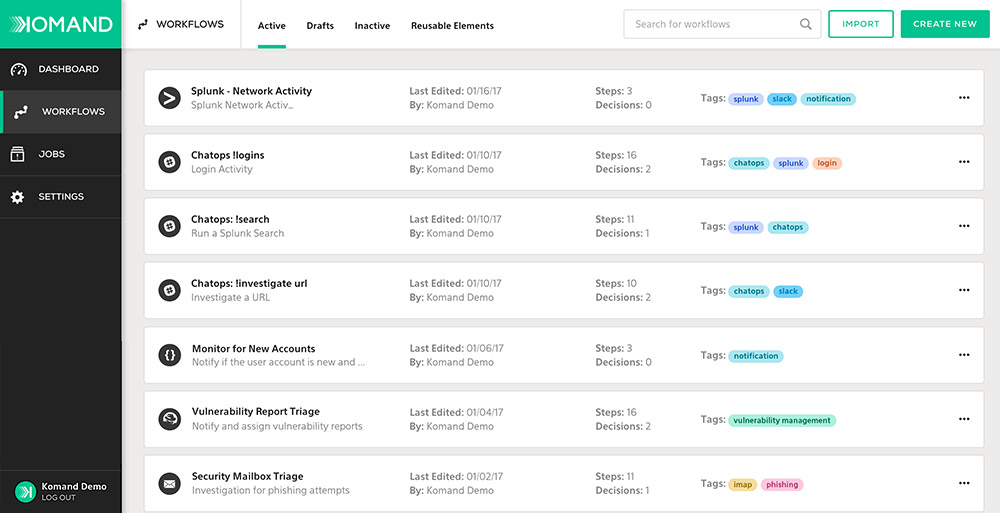
Powerful Automation, No Code Required
With workflows, you can select a trigger source, configure actions, and automate processes without writing a single line of code.

Built-in Human Decision Points
Configure human decision points within your workflows to allow for detailed analysis from your team in the most complex moments.

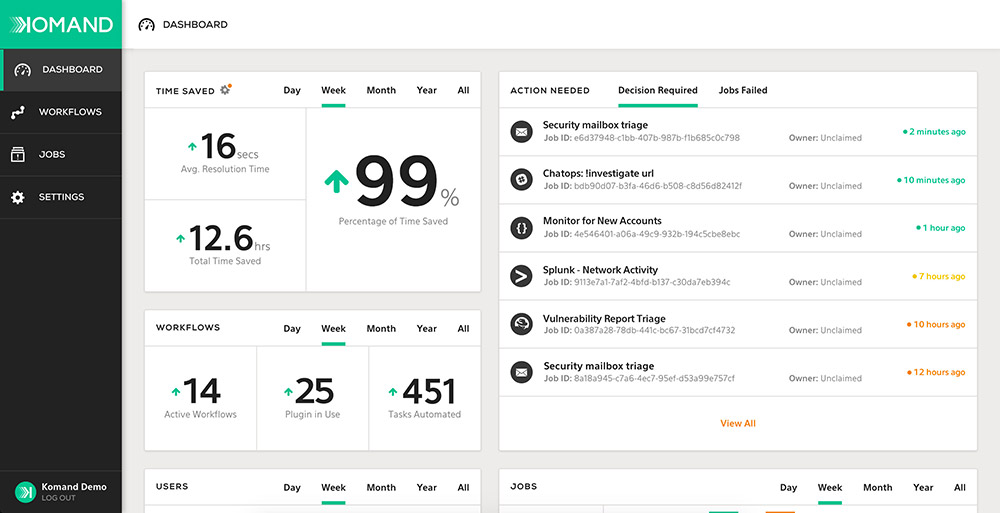
Success Benchmarks for You and Your Team
Realize the value of automation by tracking metrics including productivity gains, decisions made, number of workflow executions, and much more.

Role Based Access Control
Role-based access control allows you to easily regulate permissions and access to users across the team.

Frictionless Deployment
Deploy on-premises or in a private cloud. Either way, you’ll retain control of where, when, and how Komand is installed in your environment.

Audit Trails at Your Fingertips
With codified processes, you’ll have a comprehensive record of your workflows and jobs all in one central location.

Community Support to Get You Started Fast
Don’t reinvent the wheel when you can learn from our community of security industry pros.
Measurable Productivity Gains For Security Teams
Being able to easily connect your tools and automate current workflows can save you and your team extensive time, especially if you are working with limited resources. Beta users reported notable time savings and productivity gains, both per alert and across overall security operations. In fact, using Komand, teams can cut the time required to detect, investigate, and respond to security incidents by up to 83 percent.
Komand also acts as a force multiplier for accuracy by allowing security organizations to keep their people focused on detailed analysis, not jumping from system to system to manually fetch data—a process that can lead to a high margin of error.
Security Orchestration and Automation For Real World Problems
Komand is a practical tool for modern security teams. A team deeply ingrained in the security industry, we know how overwhelmed security operations teams are today, with more alerts and threats to investigate than ever before. We’re proud to have created a platform that is truly seamless, efficient, and cost-effective for handling today’s top use cases.
Specifically, Komand enables better and faster:
- Email phishing investigations
- Privilege escalation investigations
- User provisioning and deprovisioning
- Compromised credentials containment
- Malware investigations and containment
- Automated vulnerability assessment
- And many more!
We couldn't be more excited to release Komand to the public today and provide security teams relief from tedious tasks so they can focus on their most important work.
Want to see Komand in action? We've got a recording of our recent demo webinar.