Last updated at Mon, 11 Mar 2024 18:06:10 GMT
Security Information and Event Management (SIEM) is security's Schrödinger's cat. While half of today's organizations have purchased SIEM tools, it's unknown if the tech is useful to the security team… or if its heart is even beating or deployed. In response to this pain, people, mostly marketers, love to shout that SIEM is dead, and analysts are proposing new frameworks with SIEM 2.0/3.0, Security Analytics, User & Entity Behavior Analytics, and most recently Security Operations & Analytics Platform Architecture (SOAPA).
However, SIEM solutions have also evolved from clunky beasts to solutions that can provide value without requiring multiple dedicated resources. While some really want SIEM dead, the truth is it still describes the vision we all share: reliably find insights from security data and detect intruders early in the attack chain. What's happened in this battle of survival of the fittest is that certain approaches and models simply weren't working for security teams and the market.
What exactly has SIEM lost in this sweaty regimen of product development exercise? Three key areas have been tightened and toned to make the tech something you actually want to use.
No More Hordes of Alerts without User Behavior Context
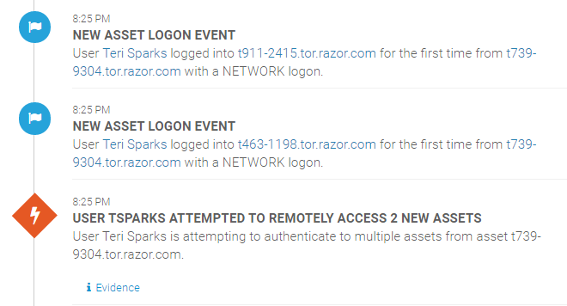
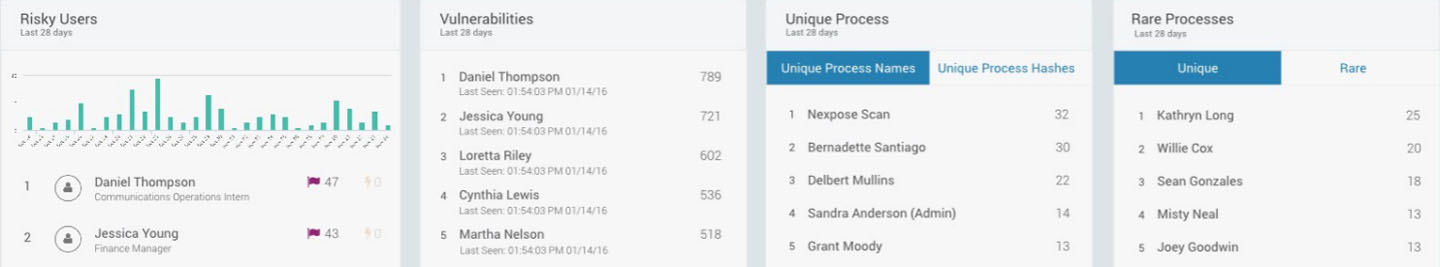
User Behavior Analytics. You'll find this phrase at every SIEM vendor's booth, and occasionally in their technology as well. Why? This entire market segment explosion spawned from two major pain-points in legacy SIEM tech: (1) too many false-positive, non-contextual alerts, and a (2) failure to detect stealthy, non-malware attacks, such as the use of stolen credentials and lateral movement.
By tying every action on the network to the users and assets behind them, security teams spend less time retracing user activity to validate and triage alerts, and can detect stealthy, malicious behavior earlier in the attack chain. Applying UBA to SIEM data results in higher quality alerts and faster investigations, as teams are spending less time retracing IPs to users and running tedious log searches.
Detections now Cover Endpoints Without Heavy Lifting
Endpoint Detection and Response. This is another super-hot technology of 2016, and while not every breach originates from the endpoint, endpoints are often an attacker's starting point and provide crucial information during investigations. There are plenty of notable behaviors that if detected, are reliable signs of “investigate-me” behavior.
A couple examples:
- Log Deletion
- First Time Admin Action (or detection of privilege exploit)
- Lateral Movement
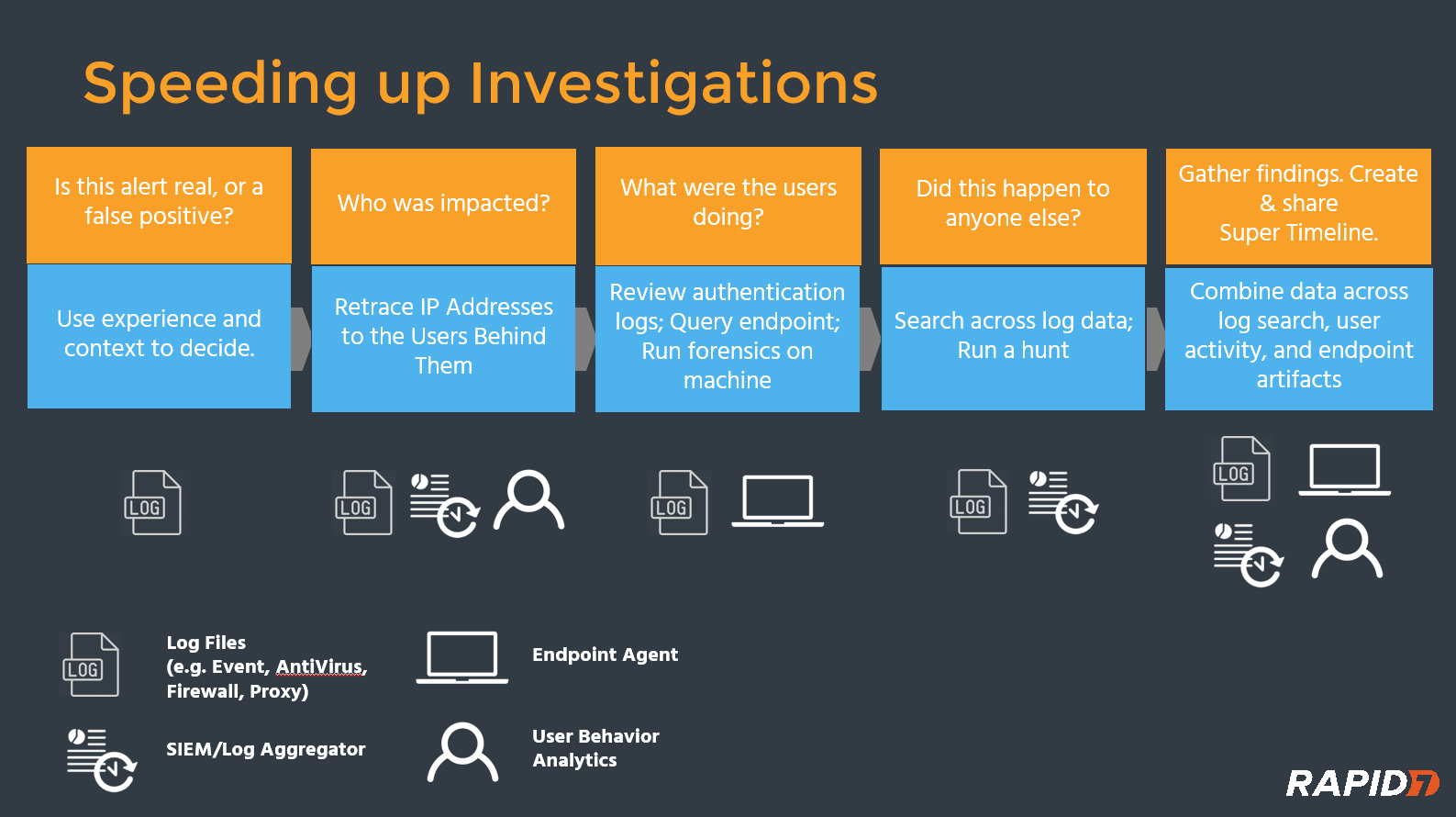
Any SIEM that doesn't offer built-in endpoint detection and visibility, or at the very least, automated ways to consume endpoint data (and not just anti-virus scans!), leaves gaps in coverage and across the attack chain. Without endpoint data, it's very challenging to have visibility into traveling and remote workers or detect an attacker before critical assets are breached. It can also complicate and slow incident investigations, as endpoint data is critical for a complete story. The below highlights a standard investigation workflow along with the relevant data sources to consult at each step.
Incident investigations are hard. They require both extended detection and response expertise (how many breaches have you been a part of?) and also data manipulation skills to get the information you need. If you can't search for endpoint data from within your SIEM, that slows down the process and may force you to physically access the endpoint to dig deeper.
Leading SIEMs today now offer a combination of Agents or an Endpoint Scan to ingest this data, detect local activity, and have it available for investigations. We do all of this and supplement our Endpoint detections with Deception Technology, which includes decoy Honey Credentials that are automatically injected into memory to better detect pass-the-hash and credential attacks.
Drop the Fear, Uncertainty, and Doubt About Data Consumption
There are a lot of things that excite me, for example, the technological singularity, autonomous driving, loading my mind onto a Westworld host. You know what isn't part of that vision? Missing and incomplete data. Today's SIEM solutions derive their value from centralizing and analyzing everything. If customers need to weigh the value of inputting one data set against another, that results in a fractured, frustrating experience. Fortunately, this too is now a problem of the past.
There are a couple of factors behind these winds of change. Memory capacity continues to expand close to a Moore's Law pace, which is fantastic, as our log storage needs are heavier than ever before.
Vendors now are offering mature cloud architectures that can securely store and retain log data to meet any compliance need, along with faster search and correlation activity than most on-premise deployments can dream about. The final shift, and one that's currently underway today, is with vendor pricing. Today's models revolve around Events per Second and Data Volume Indexed. But, what's the point of considering endpoint, cloud, and log data if the inevitable data volume balloon means the org can't afford to do so?
We've already tackled this challenge and customers have been pleased with it. Over the next few years, new and legacy vendors alike will also shed existing models to also reflect the demand for sensible data pricing that finally arms incident investigators with the data and context they need.
There's a lot of pain with existing SIEM technology – we've experienced it ourselves, from customers, and every analyst firm we've spoken with. However, that doesn't mean the goal isn't worthy or the technology has continually failed to adapt.