Last updated at Wed, 17 Jan 2024 21:37:55 GMT
Meet Lester, the Exploit Suggester
Hey there, my name is Mo ( Mohamed Sadek ). I am currently an intern at Rapid7, working with the Metasploit team in Austin. After some research, testing, and more than a few energy drinks, sinn3r (sinn3r ) and I have authored the first version of the Metasploit Local Exploit Suggester, or Lester for short. Lester is a post module that you can use to check a system for local vulnerabilities, using the local exploit checks in Metasploit, without having to fire off any of the exploits. This is a great module for scanning a system without being overly intrusive. It saves time too, since you don't have to manually search for local exploits until something works. If you have ever had to generate a report for a pen test, you've probably experienced the frustration of finding the most relevant CVEs for a particular endpoint. With the Lester, you will get exactly what you need in an easy to understand format. Let's take a closer look at what Lester can do.
Where The Vulns At?
Before you can use the local exploit suggester, you must already have a session opened on your target. It is important to note that the type of session you have on your target can change the vulnerabilities that are detected. If you are using Windows, I would recommend using Meterpreter. For all other operating systems, a shell will give you better results due to the way platform exploit matching works. For instance, Python Meterpreter is treated as implementing the 'python' platform, which can miss native platform exploits currently. We hope to improve this in the future.
PLEASE NOTE: Due to some bad spelling on my behalf, the path for Lester is actually "post/multi/recon/local_exploit_suggestor" rather than the correctly spelled "post/multi/recon/local_exploit_suggester". In next week's UI update, the correct name will be used. Sorry for the inconvenience!
Once you have opened a session, there are a few extra options you can set for improved usability:
- set verbose true
- set exitonsession false
You should also consider using the run_all_post resource script if you would like to run the exploit suggester with multiple sessions. It is well documented, so you should be able to follow along if you haven't used a resource script before: metasploit-framework/run_all_post.rc at master · rapid7/metasploit-framework · GitHub
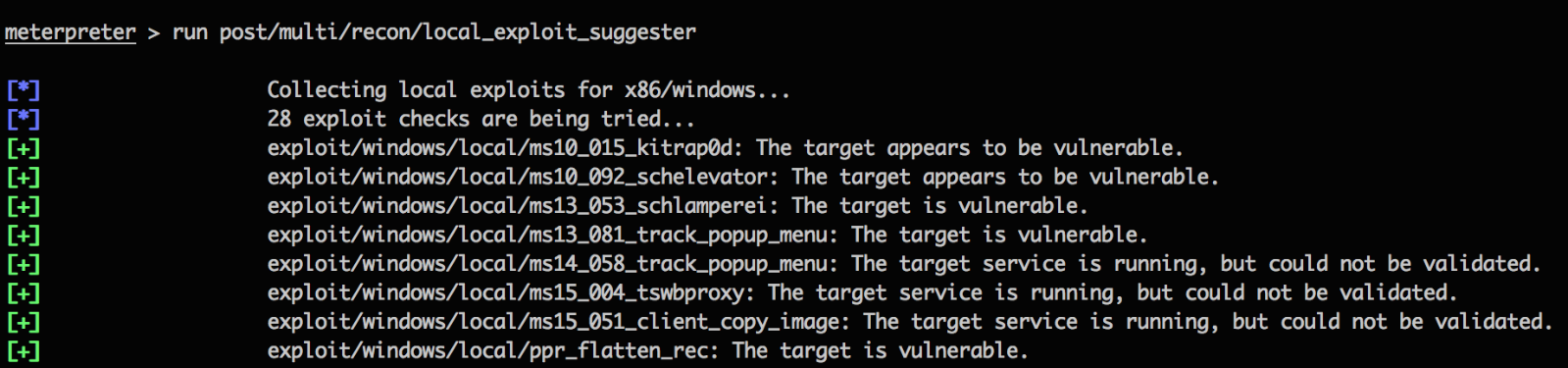
In the picture, I have run the suggester on a Windows machine using a Meterpreter session. As you can see, we get some pretty interesting information back. First, notice that we are told how many exploits are being tried. A few things are happening at this here: First, the suggester needs to make sure that the proper exploits are being checked for the architecture and operating system it's being run on. Then the suggester runs the checks for each matching exploit, as opposed to the actual exploit. Remember, the objective of the suggester is just to see what parts of a system can be exploitable.
You will notice that the exploits in the list have text next to, such as "The target appears to be vulnerable". In Metasploit Framework, we use checkcodes in conjunction with checks to categorize how effective an exploit is. In this case, we use "Vulnerable", "Appears", and "Detected" since these are checkcodes where an exploit are most likely to work. Here's how they work in a nutshell:
- Vulnerable: The check was able to use a bug or obtain hard evidence of its existence.
- Appears: When the target has the vulnerable resource available
- Detected: When the target has a vulnerable service running but the check is unable to complete.
There is also a possibility that an exploit check did not fire at all. This happens with exploits that need an option or parameter that has no default value.
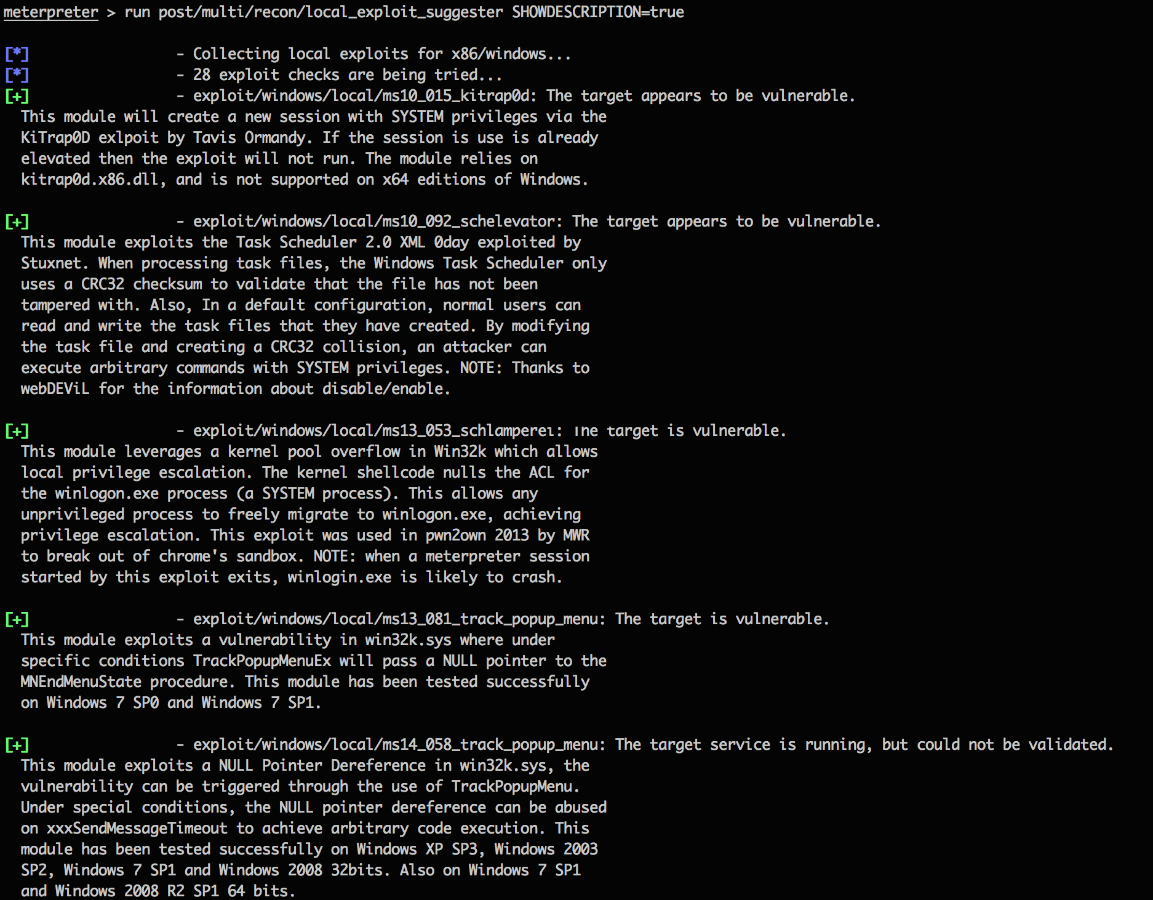
While having these results are great, there is a chance that you may have no clue what ms10_092_schelevator does or what vulnerability it is targeting. For this, enable the SHOWDESCRIPTION option to get a detailed description of the exploit. To turn on that option, add SHOWDESCRIPTION=true to the end of the run command. Your output should now look like this:
The local exploit suggester is currently available in the master branch of Metasploit Framework if you'd like to give it a whirl! If you are interested in looking at some of the code for the exploit suggester, check out the pull request on GitHub. There may or may not be a Mr. Robot reference .
https://github.com/MSadek-r7/metasploit-framework/commit/69ee5e3313581468be20999 b91a76b189160a45e
