Last updated at Wed, 07 Feb 2024 20:52:28 GMT
"I'm more comfortable with the Metasploit command line," is an objection I often hear from long-time Metasploit Framework users who are thinking about purchasing a copy of Metasploit Pro or Metasploit Express. What many penetration testers don't know is that you can use the command line in the commercial Metasploit editions, and leverage their advantages at the same time.
Reporting: The commercial Metasploit editions include one-click reporting that includes any work you have completed on the command line. No more cutting and pasting screenshots and collecting password hashes. Simply conduct your penetration test on the command line, then generate the reports - either through the command line or the Web UI. Note that the FISMA and PCI reports are exclusive to Metasploit Pro, while all other reports such as the executive report are available in all commercial editions.
Switching between Web UI and command line: You can switch between the Web UI and the command line version of Metasploit for various tasks, depending on which tool is better suited for which task. For example, you can work with the Web UI to discover the network and import scan data, switch to Metasploit Framework to do exploitation, and keep an overview of your sessions in the Web UI. You don't have to choose interface over another - just use them as two sides of the same tool.
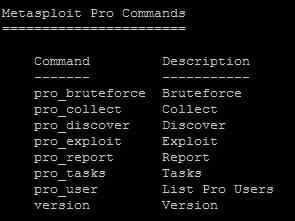 Metasploit Pro Console: With Metasploit Pro, you'll have access to powerful advanced commands in addition to the regular Metasploit Framework commands. These commands include:
Metasploit Pro Console: With Metasploit Pro, you'll have access to powerful advanced commands in addition to the regular Metasploit Framework commands. These commands include:
- pro_discover: Rather than using nmap and importing the results, this feature leverages nmap plus additional techniques to discover hosts, scan for open ports, and fingerprint operating systems and services.
- pro_exploit: While Metasploit Framework can only exploit one host, one exploit at a time, this feature can test all discovered hosts with all suitable exploits in one step. Choose exploits according to their reliability in exploiting systems safely. In addition, Metasploit Pro automatically chooses only the exploits that are appropriate for your operating system and the ports open on the specific system. Once you have successfully exploited a machine, you won't lose the session again because the Meterpreter payload supports persistent sessions and listeners so that the target machine actively re-establishes a session when it drops. You can also replay previously successful attacks to simplify verification of patch installation and configurations changes.
- pro_bruteforce: With Metasploit Framework, you can bruteforce one service at a time. Metasploit Pro offers smart brute forcing to simultaneously conduct a password strength audit on many account types and services. Before simulating a brute force attack, you can choose which account types should be tested, for example based on their lockout risk. The password guesses are based on default passwords, default and custom dictionaries, and from information gathered during the network scan. Using credential recycling and pass-the-hash techniques, you can reuse collected passwords and hashes to gain access to other systems.
- pro_collect: Gather proof of access and obtain authentication credentials to go even deeper. Unlike in the Metasploit Framework, where you have to manually collect evidence, Metasploit Pro gathers system information, screenshots, passwords, SSH keys and files, all just with one command. You can further automate the evidence collection with macros that run your choice of post-exploitation tools, e.g. a key logger. Additionally, you can extend the access of Metasploit Pro by recycling and replaying capture authentication credentials to extend access to a greater number of targets.
- pro_report: Generate reports in PDF, RTF, HTML, or XML format. Available standard reports include the Executive Summary, Detailed Audit Report, Compromised Hosts, Collected Evidence, Network Services, Authentication Tokens, Web Vulnerabilities, PCI DSS Report, and FISMA Report. You can choose to exclude sensitive information from the reports, for example you can mask username/passwords, or exclude screenshots or collected passwords.
- pro_user: With Metasploit Pro, you can collaborate in teams on any project, share results, and report on the entire team's findings using the reporting functionality. The pro_user command lists all registered Metasploit Pro users in your Metasploit instance.
Some Metasploit Pro features are not yet implemented in the command line, such as web application scanning, auditing and exploitation as well as the social engineering campaigns.
When using the Metasploit command line with the commercial features, please ensure that you are using the stable trunk, which shares the database with the Web UI, not the development trunk. To access a console that uses the stable trunk, launch the 'Metasploit Console' link in Windows or the /opt/metasploit-4.1.3/msfpro executable on Linux. For more information, see this discussion.
If you would like to test Metasploit Pro, download a free trial today!
